Azure Load Balancer Demystified: A Real-World Implementation with Linux VMs
March 13, 2026
Stop Using the Wrong VPN: A Complete Guide to WireGuard, Tailscale & ZeroTier
March 25, 2026Dutch Government Warns of Signal and WhatsApp Account Hijacking Attacks
Signal and WhatsApp are widely trusted for private communication. That trust is exactly why attackers are now focusing on them.
The Dutch intelligence services, AIVD and MIVD, have warned that Russian state actors are running a large-scale campaign to gain access to Signal and WhatsApp accounts used by dignitaries, civil servants and military personnel.
The Dutch agencies said government employees in the Netherlands have already been targeted, and they believe journalists may also be at risk. They also stressed that this is not a breach of Signal or WhatsApp themselves. The attacks are aimed at individual users.
Why this warning matters
This story matters because it shows a simple truth about modern security. Strong encryption cannot protect an account if a user is tricked into handing over access.
According to the Dutch advisory, the attackers are not relying on malware or a flaw in the apps. Instead, they are using phishing and social engineering. In plain terms, they are persuading people to share codes, scan malicious QR codes, or approve actions that give an attacker entry to their account. Once that happens, private chats, group messages and contact details may all be exposed.
How the hijacking happens
The advisory describes two main methods.
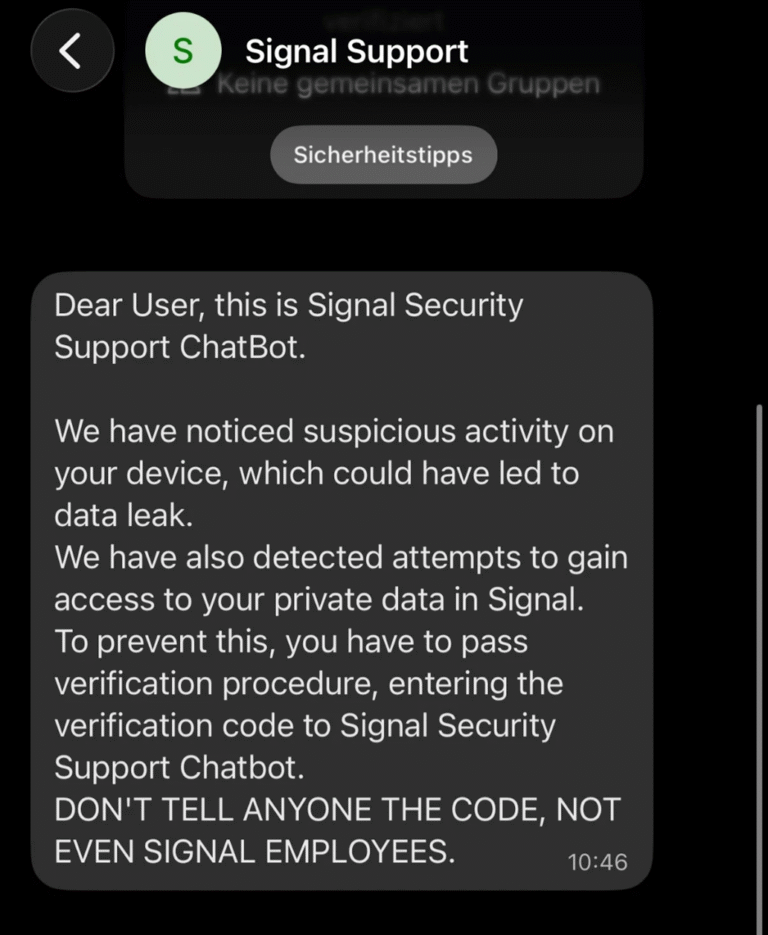
The first is classic account takeover. In many cases, the attacker pretends to be official support. Victims may receive a message that appears to come from a Signal security chatbot or support team. The message claims there is suspicious activity on the account and asks the user to complete a fake verification process. If the victim shares the SMS code and PIN, the attacker can take control of the account. The advisory says this can even defeat Signal’s Registration Lock if the PIN is revealed.
The second method uses linked devices and QR codes. Attackers persuade people to scan a QR code or click a link that looks harmless. It may appear to be a group invitation or a routine connection request. It can link the attacker’s device to the victim’s account. The Dutch warning says this tactic is being used against both Signal and WhatsApp. Once linked, the attacker may be able to read chats and even send messages in the victim’s name without being noticed straight away.
What users and organisations should do
The Dutch agencies are clear in their advice. Sensitive or classified information should not be shared through messaging apps unless those tools have been formally approved for that purpose by the organisation. That is an important point for public sector teams, journalists and businesses that deal with confidential information.
For everyday protection, the advice is practical. Users should regularly check the list of linked devices in both apps and remove anything unfamiliar. They should ignore unexpected group invitations, avoid scanning QR codes unless they are personally linking their own device, and verify suspicious requests through a different trusted channel such as a phone call or email. WhatsApp’s own guidance also tells users to review linked devices regularly.
Signal users should also enable Registration Lock and never share their PIN or verification code in a message. Signal’s support pages explain that the PIN is tied to Registration Lock, while the Dutch advisory says legitimate support will not contact users directly through a Signal message asking for codes. The advisory also recommends enabling disappearing messages where appropriate, as this can limit how much chat history is exposed if an account is compromised.
Signs that something may be wrong
One detail from the Dutch warning stands out. Users may notice contacts appearing twice in a group, slightly unusual names, or accounts suddenly showing as deleted. These can all be signs of compromise. If that happens, it should be checked outside the app rather than through the same chat thread.
Final thoughts
The Dutch government’s warning is a reminder that secure apps still depend on secure behaviour. Attackers do not always need advanced malware. Sometimes they only need a believable message and a distracted user.
For readers, the lesson is simple. Do not trust unexpected support messages. Do not share verification codes. Check linked devices often. And treat any unusual request inside Signal or WhatsApp with caution. In many cases, good habits are still the strongest defence.
Need help improving your cyber security content, technical blog posts, or IT-focused website copy? Visit my Contact Me page and let’s discuss how I can help your business create clear, practical, and search-friendly content.

