
Proxmox Ceph vs ZFS: Which Storage Should You Choose in 2026?
March 6, 2026Azure Load Balancer Demystified: A Real-World Implementation with Linux VMs
March 13, 2026The Micro-Burst Epidemic: API Security Best Practices for 2026
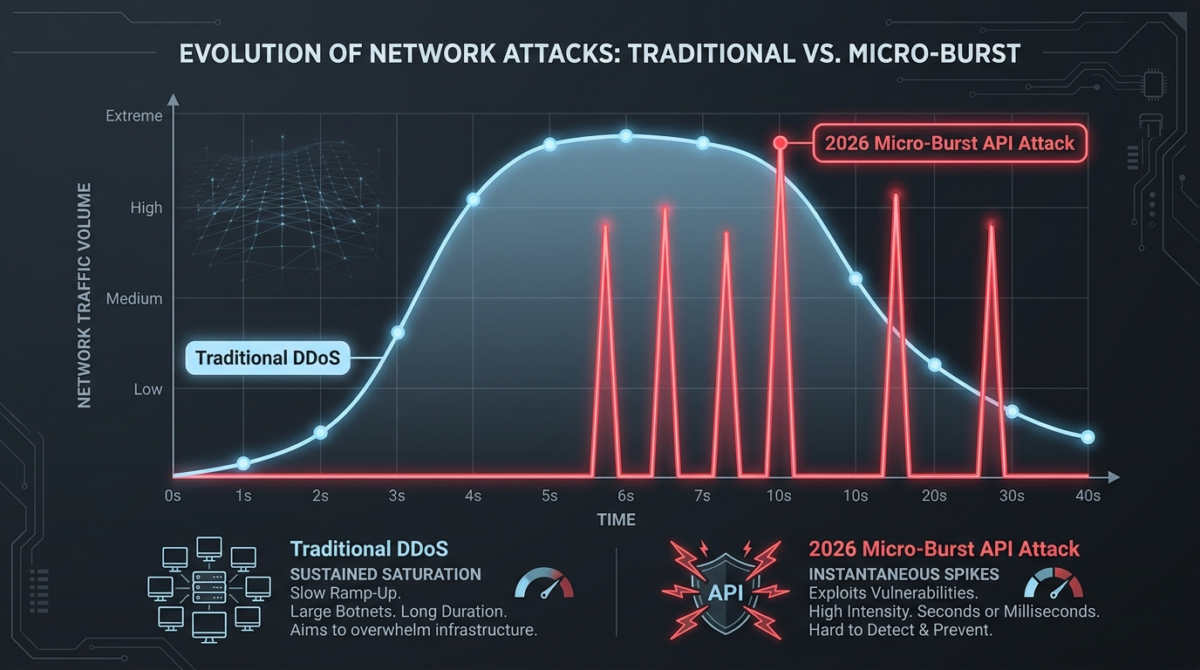
The Distributed Denial-of-Service (DDoS) threat has fundamentally and irrevocably changed. The automation of DDoS attacks has become incredibly dangerous as AI tools are increasingly used to launch, monitor, and adjust campaigns on the fly. Among the most damaging trends hitting our servers this year is the rise of the “micro-burst” attack.
These hit-and-run tactics operate at a speed and scale that humans simply cannot match. Instead of the prolonged, volumetric floods we used to see, attackers are now blasting Application Programming Interfaces (APIs) with sudden, violent spikes of traffic that vanish almost as quickly as they appear.
Legacy approaches that rely on human-in-the-loop defenses or standard hardware probes are now completely obsolete against these tactics. Here is a look at why your APIs are in the crosshairs, and the exact API security best practices in 2026 you need to harden your infrastructure.
Why Your APIs Are the Perfect Target
APIs serve as the direct bridge to your most sensitive backend databases. When an attacker launches a micro-burst against a resource-intensive API endpoint, even a brief surge can saturate the link or cause excessive backend loads.
Because these attacks happen so fast, traditional scrubbing centers and traffic analyzers fail to block them in time. A massive wave of traffic hits, maxes out the CPU on your VMs, drops legitimate client connections, and then the attackers disappear before your firewall even triggers an alert.
Worse, these automated bursts are often used as a smokescreen to mask secondary attacks, like credential stuffing or rapid vulnerability scanning, within the chaos.
To survive this, you have to rethink how traffic flows through your hypervisors and gateways.
API Security Best Practices for 2026 Defenses
Next-generation DDoS security requires a new architecture built on a foundation of high-speed, fully automated, AI-driven defense. Here is how to lock down your environment against the micro-burst epidemic.
- Deploy Inline, Automated Mitigation: You must move away from manual intervention. Your defense must be intelligent enough to understand the context of traffic, not just its volume, and integrated directly into the network fabric. Experimental hardware systems have shown that suppressing attack traffic within 30 milliseconds is necessary to prevent dropping normal, legitimate traffic during a burst.
- Enforce Strict Input Validation: Treat every single input as untrusted, including headers and URLs. Reject malformed JSON early to avoid parser exploits, and always validate incoming data using strict schemas. This ensures that even if a burst of traffic makes it to your gateway, the malicious payloads never reach your database layer.
- Implement Granular Rate Limiting and Throttling: Basic IP blocks are insufficient against modern, distributed botnets. You must implement robust rate limiting and throttling to manage authentication and prevent automated abuse.
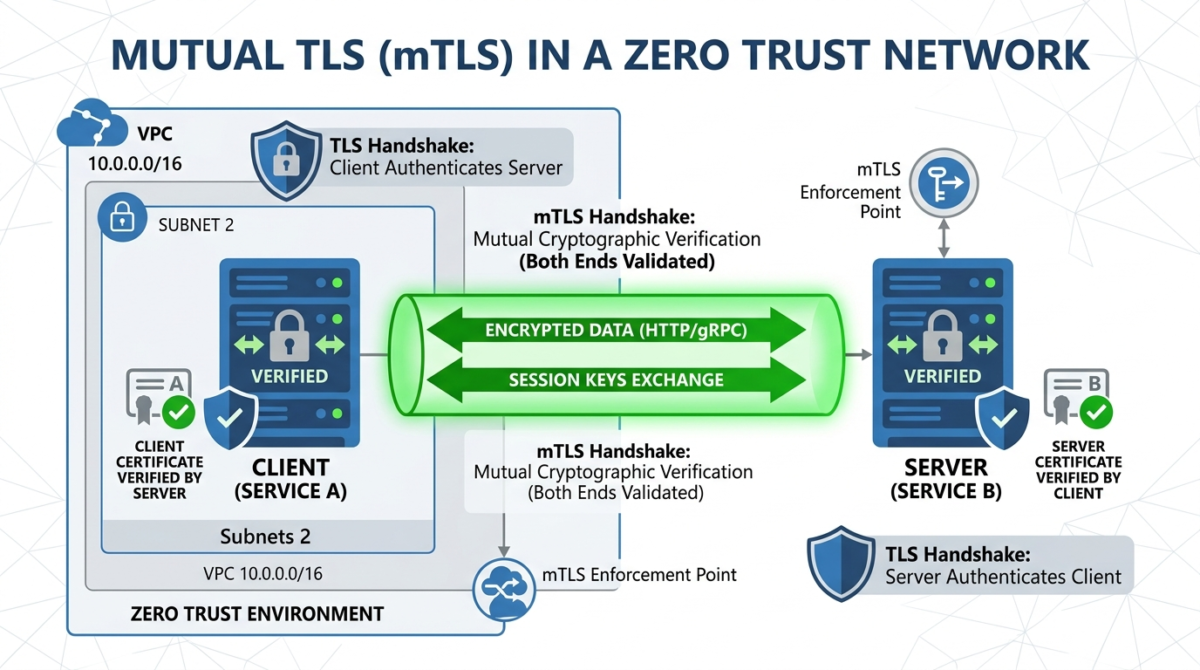
- Shift to Mutual TLS (mTLS): Never allow plaintext HTTP, even internally. Use mutual TLS (mTLS) for service-to-service calls to cryptographically verify both sides of the connection. This principle of encrypting everything is critical for maintaining a zero-trust architecture across your Proxmox clusters and cloud instances.
As attackers leverage automation to launch devastating hit-and-run attacks, our manual security interventions are no longer enough. Hardening your API gateways, enforcing strict schema validation, and utilizing automated inline mitigation are absolute requirements for running highly available infrastructure today.
Are you struggling to mitigate automated API attacks, or do you need a hand architecting resilient, zero-trust infrastructure across your cloud and on-premise servers? I am here to help. Head over to my Contact Me page, drop the details of your setup, and let’s start a conversation about securing your environment.

